meshDETECT® is pleased to announce that it has been granted a sixth wireless blockchain patent from the United States Patent and Trademark Office for U.S. Patent 11,956,383 entitled “Systems and Methods For Blockchain Wireless Services In a Controlled Environment.” This is our twelfth patent granted overall. The claims in our latest blockchain patent are directed toward a multi-blockchain system to secure, manage, and validate forensic data in controlled environments such as prisons and jails Digital […]
meshDETECT
This latest patent protects the intellectual property necessary to enhance inmate wallet functionality, improve transaction security, and expand services rental and payment functionality via smart contracts, dAPPs and custom tokens.
meshDETECT® is pleased to announce that it has recently received a notice of allowance for our third wireless blockchain patent from the United States Patent and Trademark Office (USPTO) for U.S. Patent Application Number 16/953,676 entitled “Systems and Methods For Blockchain Wireless Services In a Controlled Environment.” A notice of allowance from the United States Patent and Trademark Office is a written notification that a patent application has cleared internal review and is pending issuance. […]
The claims in this latest patent are directed toward managing commissary transactions using blockchain and smart contracts, for token management supported by a blockchain and for the enforcement of regulations in a controlled environment.
meshDETECT® is pleased to announce that it has recently received a notice of allowance from the United States Patent and Trademark Office (USPTO) for U.S. Patent Application Number US16/386,248 entitled “System and method for controlling, monitoring and recording of wireless telecommunications services in penal institutions.” This is our sixth patent overall and the fifth in this family of patents. A notice of allowance from the United States Patent and Trademark Office is a written notification […]
meshDETECT® is pleased to announce that it has recently received a notice of allowance from the United States Patent and Trademark Office (USPTO) for U.S. Patent Application Number 16/517620 entitled “Systems and Methods For Blockchain Wireless Services In a Controlled Environment.” A notice of allowance from the United States Patent and Trademark Office is a written notification that a patent application has cleared internal review and is pending issuance. This fifth patent expands our Secure […]
meshDETECT® is pleased to announce that it has recently received a notice of allowance from the United States Patent and Trademark Office (USPTO) for U.S. Patent Application Number 15/700,144 entitled “System and method for controlling, monitoring and recording of wireless telecommunications services in penal institutions.” A notice of allowance from the United States Patent and Trademark Office is a written notification that a patent application has cleared internal review and is pending issuance. This fourth […]
meshDETECT® is pleased to announce that it has recently received a notice of allowance from the United States Patent and Trademark Office (USPTO) for U.S. Patent Application Number 14/945,145 entitled “System and method for controlling, monitoring and recording of wireless telecommunications services in penal institutions.” A notice of allowance from the United States Patent and Trademark Office is a written notification that a patent application has cleared internal review and is pending issuance. This patent […]
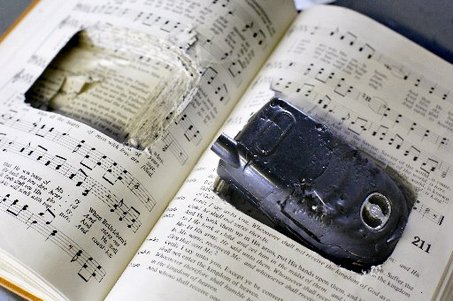
After last year’s announcement by the CDCR that they would halt the deployment of the managed access systems touted to stop the supply of contraband cell phones into California’s state prisons, the Department of Corrections and Rehabilitation has now announced it is installing 272 more metal detectors, 68 X-ray machines to scan packages, 103 low-dose X-ray scanners, 170 hidden surveillance cameras, 34 devices to decrypt and analyze cellphones, and 272 scanners that detect magnetic signals […]
The FCC has frequently advocated for competition in the provision and availability of inmate communications services (ICS) in prisons and jails. In its Second Report And Order And Third Further Notice Of Proposed Rulemaking (NPRM) adopted on 10/22/15, it wrote, “While we adopt regulations in this Order to correct failures in the ICS market, the Commission generally prefers to rely on competition over regulation. We seek additional comment on whether there are ways to promote […]
meshDETECT® is pleased to announce that it has recently received a notice of allowance from the United States Patent and Trademark Office (USPTO) for U.S. Patent Application Number 13/931,850, which is a continuation of our first patent entitled “System and method for controlling, monitoring and recording of wireless telecommunications services in penal institutions.” A notice of allowance from the United States Patent and Trademark Office is a written notification that a patent application has cleared […]
Innovation, especially technology innovation, requires a willingness to challenge accepted approaches to problems as well as entrenched industry “truths”. This nontraditional thinking is best captured by a quote from hockey great Wayne Gretzky, “I skate to where the puck is going to be, not where it has been.” Back in June of 2011, we issued a press release announcing the introduction of the meshDETECT Secure Prison Cell Phone Solution. In the press release we said, […]
Today I participated in the FCC’s Workshop on Inmate Calling Services Reform on the New Technologies panel to consider new and emerging forms of communications in correctional settings beyond the traditional wireline telephone call. Below is the text of my opening statement: As this workshop is focused on inmate calling services and this panel is specifically targeted to new technologies, I would like to focus my opening comments on a new solution to the problem […]
The United Kingdom’s Ministry of Justice has determined that managed access jamming of contraband cell phones is too expensive and has commissioned “research to explore the use and demand for illicit mobile phones amongst the prison population” in order to facilitate the “development of a new mobile phone strategy to: (i) manage prisoner communications, (ii) reduce and control criminal activities and (iii) reduce expenditure on equipment and the need for time-consuming searches.” The aim […]
With Global Tel*Link all but announcing at the recent Corrections Technology Association Annual Meeting its intention to offer mobile services in prisons, now may be the time to consider the best technology architecture for such deployments for those prison administrators who see the potential benefits of a secure prison cell phone solution. There are essentially two ways to provision wireless personal communication devices, such as prisoner tablets, in a prison environment. In its presentation, Global […]
We post this summary of Global Tel*Link’s upcoming presentation “Mobility In Corrections” at the Corrections Technology Association (CTA) 2013 Annual Technology Summit, without comment… It is a question of when, not if, are secure mobile phones and/or tablets are used by inmates in a correctional setting. There are natural applications for the use of secure mobile phones include; telephone calls, video calls, music and email using the embedded capabilities of today’s mobile phones. Additional applications […]
meshDETECT® is pleased to announce that it has recently received a notice of allowance from the United States Patent and Trademark Office for a patent application entitled, “System and method for controlling, monitoring and recording of wireless telecommunications services in penal institutions” covering its Secure Prison Cell Phone Solutions™. A notice of allowance from the United States Patent and Trademark Office is a written notification that a patent application has cleared internal review and is […]
meshDETECT, Control Contraband Cell Phones Without Investment This presentation on controlling contraband cell phones in prison provides an overview of the problem, of the supply-side strategies currently deployed and of meshDETECT’s secure prison cell phone solution. To learn more, also download our whitepaper, “Reducing the Demand for Contraband Cell Phones in Correctional Facilities.”
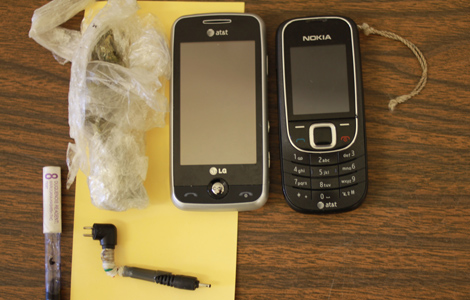
We agree that unmonitored contraband cell phones don’t belong in prison cells, but we believe that a secure prison cell phone solution such as meshDETECT can not only reduce the demand for smuggled cell phones but also enhance safety, decrease recidivism and increase prison revenues. Download our whitepaper “Reducing the Demand for Contraband Cell Phones in Correctional Facilities” to learn more. Sarah Pender orchestrated her escape from Rockville Correctional Facility in 2008 using contraband cellphones […]
This article touches on just about all the key issues and challenges facing prisons, detainees and families when talking about the contraband cell phone problem. Key quotes from the article: Availability – “cellphones are just everywhere in prison nowadays…. It’s easy to borrow one from a guy”. “This year, guards (in California) are on pace to seize about 15,000 phones — nearly one for every 11 inmates.” Corruption – “Almost as troubling as prisoners gaining […]
Even a person with a long history of crimes committed wants to keep in touch with and talk to her children. This person paid to use a smuggled cell phone to call family members. Now due to being caught with the contraband cell phone, she will spend more time in prison. There is a legitimate need for meshDETECT’s secure cell phone service in prisons. A woman serving time in the Accomack County jail who was […]
This recent editorial on contraband cell phones from the LA Times advocates making the penalties for smuggling cell phones into prisons harsher. And perhaps tougher penalties for those guards and prison staff who are caught smuggling prison cell phones would act as deterrence for some. But with over 10,000 cell phones confiscated in California jails last year alone, it is unlikely a new law will significantly stem the tide of smuggled wireless phones into prisons. […]
This article is about yet another prison guard caught smuggling a contraband cell phone into jail. Given the high price paid by inmates for an illegal cell phone, the corruption of prison guards has become all to commonplace. A reduction of the contraband value of smuggled cell phones through the deployment of the meshDETECT secure prison cell phone solution will change the economics of this problem and reduce prison cell phone smuggling without the high […]
The National Geographic’s Hard Time TV series most recent episode is about smuggled prison cell phones. It’s called Cellphone War and below are some facts from the show. The meshDETECT secure cell phone service addresses the legitimate inmate desire for family contact and therefore reduces the contraband value of smuggled prison cell phones. CELL PHONE WAR FACTS: Did you know that the ownership of a cell phone behind bars is prohibited in both state and […]
This article is a discussion of the problem of contraband cell phones in Ohio prisons. Same issues as everywhere else with the same lack of solutions. However, a secure cell phone service is a solution to the contraband prison cell phone problem. With meshDETECT, the demand for illegal wireless devices is reduced, thereby reducing the contraband value of smuggled cell phones for those who supply them. That means less reward for the same risk and […]
This article discusses the methods by which prisoners can currently make telephone calls in a Dayton, OH county jail. An interesting quote from the article is, “Monies made from jail commissary sales, including calling cards, are utilized to support the current jail inmate population.” The meshDETECT secure prison cell phone service is another means by which prisoners can stay in contact with friends and family. It also provides a revenue stream for cash-strapped prison systems […]
An article discussing a New Zealand prison’s plans to install landlines in each prisoner’s cell, similar to what has been done in two British prisons. The reason it is being considered is because, according to the article, “Evidence shows that prisoners are less likely to re-offend if they keep in touch with their families and have good family support when they are released.” Wouldn’t a secure prison cell phone service like meshDETECT be a simpler […]
The smuggling and illegal use of contraband cell phones in prisons in the United States has corrections administrators and officers at a disadvantage as wireless detection technologies have not kept pace with the surge in illegal cell phones in prisons. It is estimated that over 10,000 illegal cell phones were seized during 2010 in California state prisons alone. Signal jamming technologies are proving to be too expensive, and the time and cost demands on prison […]
Officials tasked with controlling the waves of contraband cell phones in prisons are at a disadvantage. Their options include costly new investment in complex jamming technologies, increasing staff, more physical searches, or new processes; all added to an already over burdened work force. In each case, cell phone control will be expensive, and results will be elusive. meshDETECT is a cell phone access and control platform that was developed to satisfy the access control and […]
These searches are necessary because the high contraband value of smuggled prison cell phones has a corrupting influence on guards and staff. With prisoners paying as much as $1000 per contraband cell phone, the temptation to smuggled wireless devices is too much for some prison staff. We beleive part of the solution is to lower the contraband value of the smuggled cell phones by implementing the meshDETECT secure cell phone service solution. Random staff searches […]
This article discusses how as prisons try to block unauthorized cell phone use, companies are developing systems that cost over $1 million to address the problem. This is cost that will be passed on to the taxpayer if prisons adopt this technology. By adopting the meshDETECT secure prison cell phone solution, prisons and taxpayers will avoid this cost and reduce prison cell phone smuggling and the value of contraband prison cell phones. The Bloods street […]
According to this news article, possession of contraband prison cell phones will be a felony in Alabama prisons and prison cell phone detection technology will be allowed if an Alabama bill passes. Rather than spend state funds on prison cell phone jammers, Alabama should consider a secure prison cell phone solution such as meshDETECT. A Senate committee today approved a bill that would give the state Department of Corrections new powers to keep cell phones […]
This news item highlights the corrosive effects the demand for contraband prison cell phones has on prison guards and other prison employees. Because the demand for illegal cell phones is so high, guards are paid to smuggle the phones into the jails. The demand for contraband prison cell phones would be significantly lessened by the introduction of secure prison cell phones such as those offered by meshDETECT. A former state correction officer from Avenel pleaded […]
The “legitimate” use of prison cell phones by prisoners to stay in contact with friends and family is highlighted in this article. Amazingly over 10,000 contraband prison cell phones were confiscated in California prisons in 2010. That is lost revenue the state could have earned by deploying the meshDETECT Secure Prison Cell Phone Solution. Bidders on the upcoming California prisons contract for inmates’ pay phone service will be asked to include equipment to block cellphone […]